ClevGuard Support: Monitor Devices with Others' Permission.
Have you ever wondered how hackers gain unauthorized access to computers, silently infiltrating networks and compromising sensitive information? The answer lies in the fascinating realm of hacking with IP addresses.
In this era of interconnectedness, every device is assigned a unique IP address. Understanding the methods employed by hackers becomes crucial in order to safeguard our digital lives. So, how exactly can someone hack a computer using an IP address? In this article, we will discuss various methods on how to hack a computer with IP. By the end of this guide, you will have a clear understanding of the hacking process.

In this article:
Part 1. Introduction to IP Addresses
An IP (Internet Protocol) address is a unique numerical label assigned to each device connected to a computer network that uses the Internet Protocol for communication. It serves two main functions: identifying the host or network interface and providing the location of the host in the network.
Knowing someone's IP address can provide a hacker with a starting point to launch an attack on their computer.
Part 2. Understanding the Challenges in Hacking a Computer with IP
However, hack a computer with IP address is not an easy task, as there are numerous challenges and security measures that must be overcome. Hack a computer with IP address can be difficult due to several factors:
- Firewalls and Security Measures: Most computers have firewalls and security software in place to protect them from unauthorized access. These security measures can block hackers from connecting to the target computer using its IP address.
- Dynamic IP Addresses: Many internet service providers (ISPs) assign dynamic IP addresses to their customers. This means that the IP address of a target computer may change periodically, making it harder for a hacker to maintain a connection.
- Ports and Services: To hack a computer with IP address, a hacker must first identify open ports and running services on the target machine. This often requires scanning thousands of ports, which can be time-consuming and may trigger security alerts.
Part 3. Methods to Hack a Computer with IP Address
Despite these challenges, there are several methods that can be used to hack a computer with IP address. In this section, we will discuss two such methods and their respective procedures.
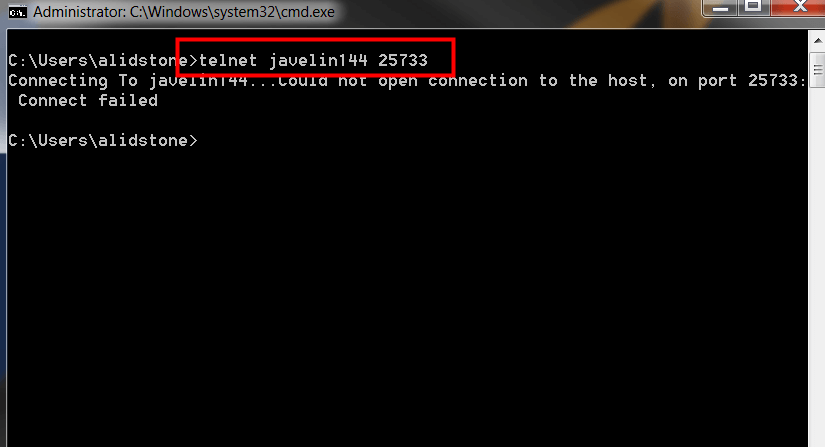
1 Using Telnet
Telnet is a protocol used for remote access to computers over a network. It can be used to control a computer through a command-line interface (CLI) by connecting to its IP address. However, Telnet connections can be easily detected and blocked by firewalls and security software. Additionally, many modern systems do not enable Telnet by default due to its inherent security risks.
How to use Telnet to hack a computer with IP:
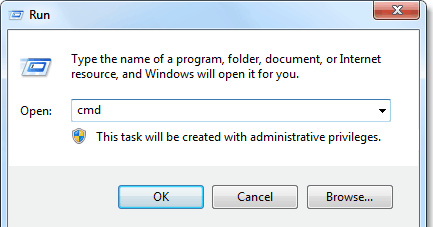
- Open a terminal or command prompt on your computer by pressing the "Windows + R" key.
- Type "telnet [target IP address] [port number]" and press Enter.
- If the connection is successful, you will be prompted to enter a username and password. You can try common default credentials or use brute-force techniques to guess the correct credentials.
2 Using Command Prompt and NetBIOS
NetBIOS is a networking protocol used for communication between computers in a local area network (LAN). It can be exploited to gain unauthorized access to a computer by using its IP address and the command prompt. Below is a brief step-by-step guide, to use this method correctly, please familiarize yourself with Command Prompt and NetBIOS protocols.
How to use NetBIOS to hack a computer with IP:
- Open Command Prompt and execute "nbtstat -a [target IP]" to retrieve NetBIOS information.
- Note down the "MAC Address" of the target computer.
- Use the command "arp -a" to obtain the MAC address-to-IP mapping and craft a malicious payload or exploit using this information.
- Launch the attack by sending the payload to the target computer to gain unauthorized access and control over the hacked computer.
![nbtstat -a [target IP]](https://images.clevguard.org/clevguardorgen/assets/images/article/nbtstat-a-command.png)
The Limitations of Traditional Hacking Methods
While the methods described above can be used to hack a computer with IP address, they come with several limitations:
Part 4. Hack a computer without IP or Technical Expertise
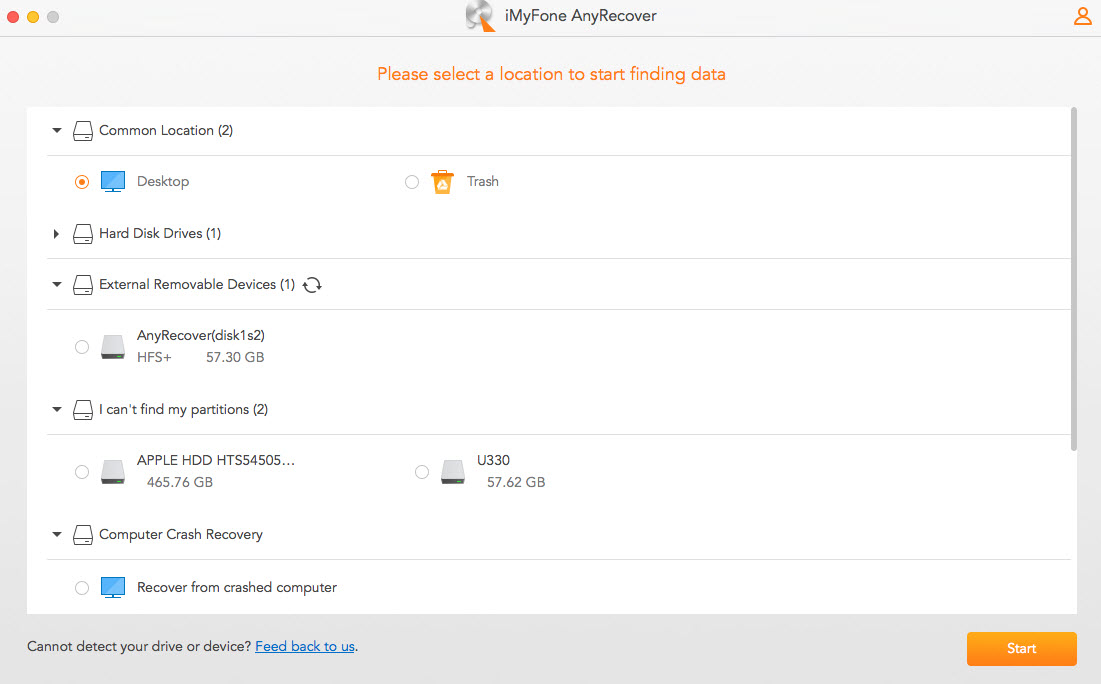
Considering the limitations and challenges associated with traditional hacking methods, it is essential to explore a more efficient and secure alternative.
If you're interested in finding out how to hack a computer without an IP address, put MoniVisor on your list.
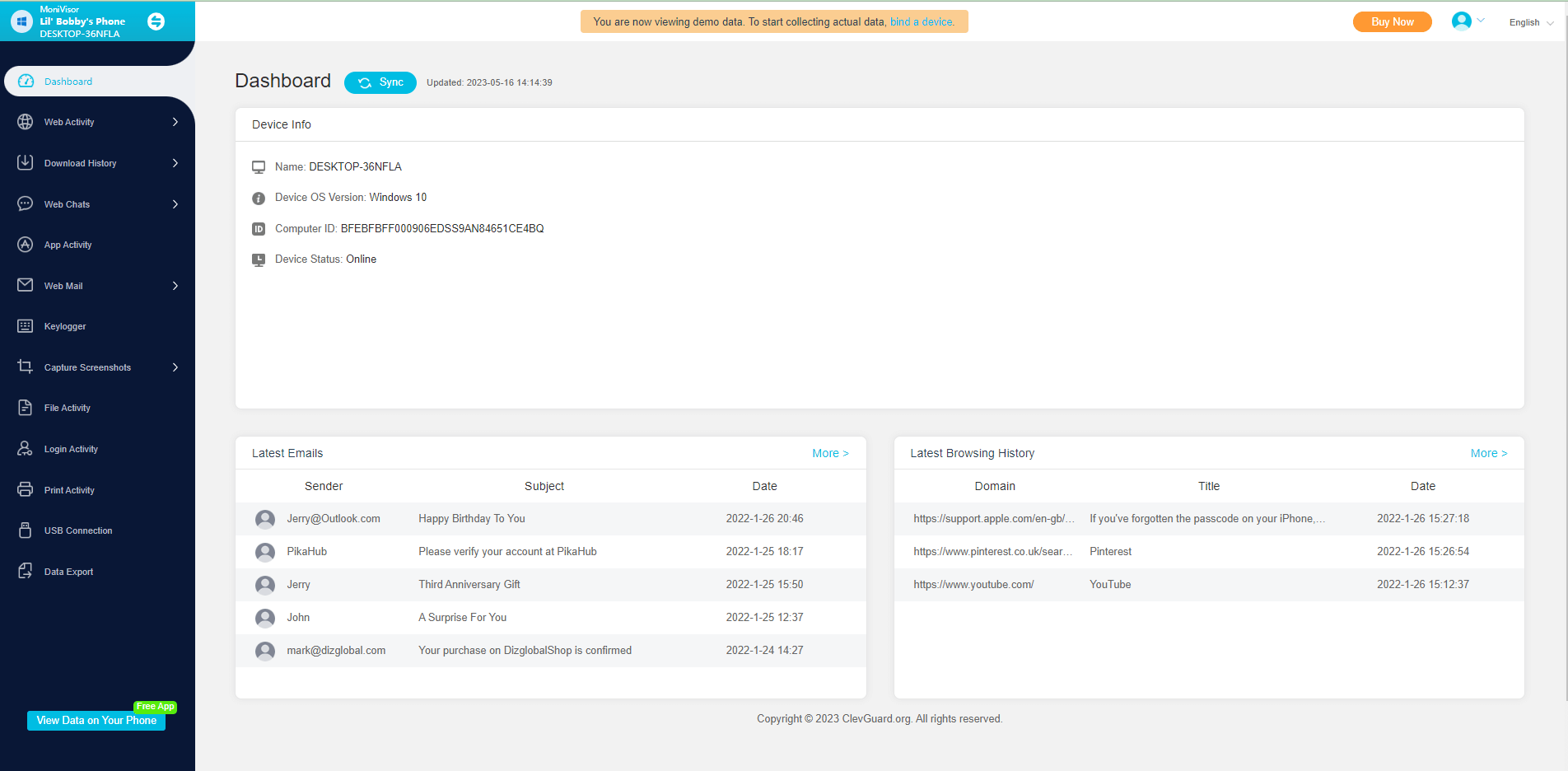
MoniVisor is a professional computer monitoring tool designed to remotely hack a computer without any technical knowledge. What’s more important, it provides comprehensive online activity monitoring such as social media app monitoring, auto-screenshot, and keystroke recording.

Features of The Best Computer Hacker-MoniVisor:
- Social Media Monitoring: Record conversations on Facebook, WhatsApp, Twitter, Instagram, and Skype without logging into their accounts.
- Internet Activity Tracking: Track all browsing and download history across multiple browsers, including Chrome, Firefox, Opera, and Microsoft Edge.
- Automatic Screenshot Capture: Capture screenshots of the target computer's screen every 15 seconds for 5 minutes.
- Keystroke Recording:Record all keystrokes with 100% accuracy using the built-in keylogger feature.
- Email Monitoring View all details of the emails received or sent on the computer
- App Activity Tracking: Exactly know the last use time of a specific app.
- Login Activity Monitoring: Report on the time and place of each Internet connection.
Using MoniVisor to hack a computer is a simple three-step process:
Step 1: Register an account with MoniVisor by clicking on the Monitor Now button.
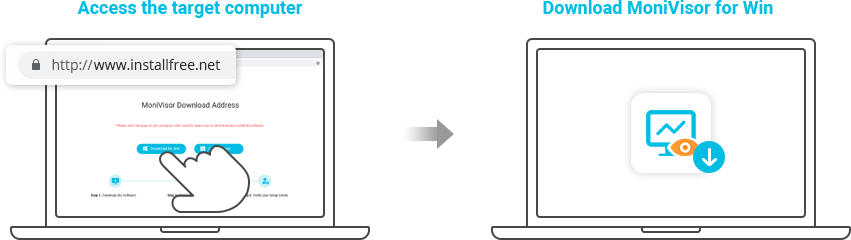
Step 2: On the target computer, go to www.installfree.net to download MoniVisor and then complete settings.
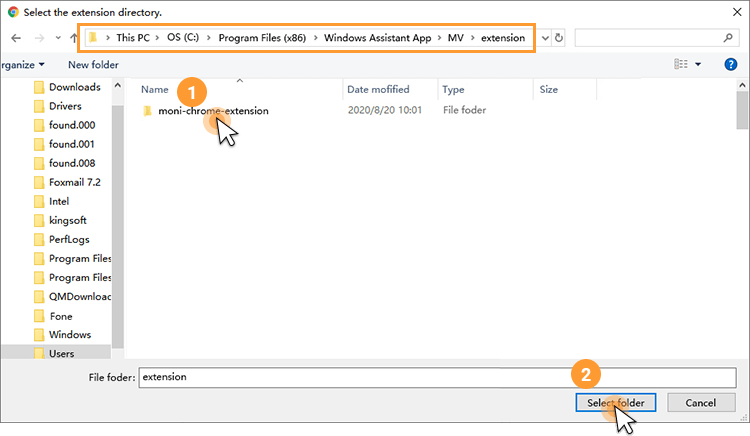
Step 3: To monitor the online activity, remember to also download the MoniVisor for Win browser extension. However, this step is optional.
Step 4: Lastly, sign up your account on clevguard.org and bind your device on MoniVisor dashboard. Afterward, you will be able to view someone's computer data remotely and secretly. Try it right now!
Why choose MoniVisor to hack your computer instead of hacking with IP?
There are numerous advantages to using MoniVisor for computer hacking as compared to using Ip address.
User-friendly interface: MoniVisor has an intuitive and user-friendly interface, you don't need to know professional knowledge of computer technology.
Comprehensive monitoring: MoniVisor offers complete and thorough monitoring of a target computer's activities, including keystrokes, internet browsing history, and chat conversations.
Stealth mode: This means that it is undetectable and cannot be removed by the target person.
Remote access: With MoniVisor, you can remotely access the target computer from anywhere and at any time, allowing you to monitor the computer's activities without being physically present.
Start Hacking Another Computer Right Now!
Summary
In this comprehensive guide, we explore the various ways to hack a computer with IP. Due to the various limitations of traditional hacking methods. MoniVisor offers a simple, effective, and legitimate alternative for individuals looking to monitor a target computer without any technical expertise.
Whether you want to figure out how to hack a computer or you're looking for other ways to keep them safe, MoniVisor is the best computer monitoring software for you. And it does way more than you think. Click the button below to try it for free now!







 Store
Store